Threat Detection & Protection
Detect and prevent cyber threats – before they can strike – and respond to problems with speed and accuracy.

Stay ahead of lurking threats.
Safeguard patient data.Strengthen your healthcare cloud with advanced threat protection that doesn’t wait around for an attack or incident to happen. Proactive threat detection and protection give you the tools to shield sensitive healthcare information from evolving cyber dangers.
Detect and neutralize threats before they cause harm.
Leverage advanced analytics and automated tools for 24/7 monitoring.
Ensure compliance with industry-leading security frameworks.
Keep your systems secure with continuous monitoring, real-time threat response, and five times faster mean time to resolve (MTTR) than healthcare orgs that do it themselves.
With end-to-end visibility into threats and a team of certified experts by your side, you can focus on delivering exceptional healthcare without worrying about cybersecurity gaps lurking around the corner.
Here’s how ClearDATA works for you:
Threat detection
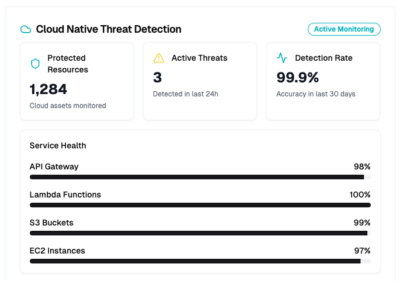
Cloud platform protection
Identification and mitigation
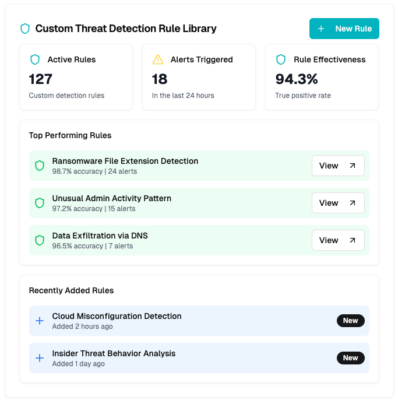
Integrated automated threat detection
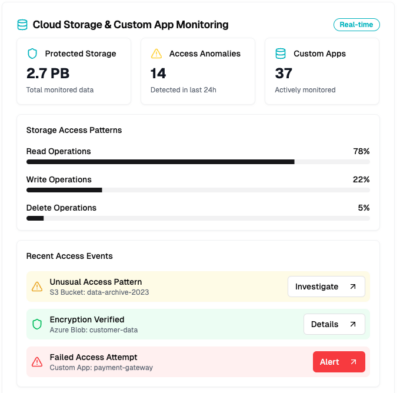
Get 24x7x365 security monitoring and protection in AWS, Azure, and Google cloud environments.
We apply the latest threat intelligence and advanced analytics to continuous security monitoring and alerts, allowing real-time detection and response to security threats.
Our CyberHealth™ platform ensures you have the auditable and actionable information you need for security insights, visualizations, data analytics, and risk management.
Credentialed. Celebrated. Certified.