Request a Consultation
If a corporation is considered a legal entity, then it should have the right to ask itself an existential question: “Who am I?”
Will its daily reality involve using its talents and competencies to fulfill its lifelong mission—or will it become sidetracked? Everywhere across the entire band of the healthcare spectrum, organizations continuously struggle with the complexity of regulatory interpretations. It’s an overly time-consuming task when you consider that the bulk of each organization’s time should be devoted to its larger purpose—making the world a healthier place.
When it comes to protecting patients’ health information, security and compliance are imperatives, but they are also complicated endeavors.
And why shouldn’t they be? HIPAA was written over twenty years ago when the cloud was hardly a thought in the day of most healthcare leaders. It was certainly not in the minds of the drafters of the legislation. But the intent of the legislation is critically important to uphold.
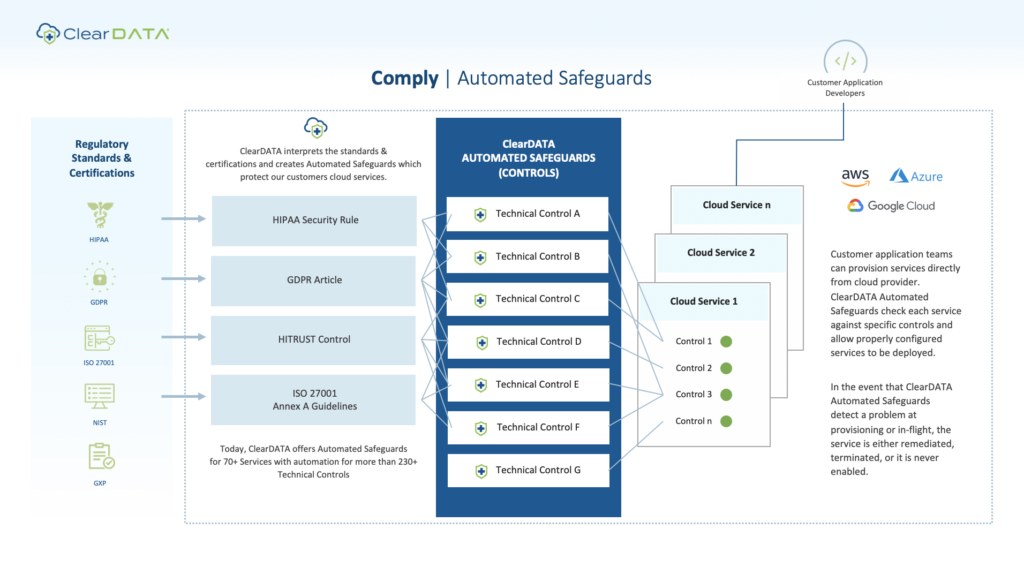
ClearDATA Comply™ can help your organization smooth out the complexities surrounding security and compliance by allowing your developers to remain safely within regulatory standards and certifications—HIPAA, GxP, GDPR, etc.—as they use the cloud to develop and create. Your developers want to take advantage of the cloud’s cutting-edge platform and services, and with ClearDATA Comply Automated Safeguards, they can do so without putting compliance at risk—and without altering the environment. If an instance falls out of compliance, ClearDATA takes appropriate action to remediate it automatically—eliminating the risk of human error and helping keep your data safe. Let’s take a deeper look at how Automated Safeguards can benefit your organization.
Learn more about ClearDATA Comply
Why Automated Safeguards Matter
In healthcare, security and compliance are urgently important. And that’s why Automated Safeguards matter.
Automated Safeguards leave your organization’s most creative minds free to branch out and innovate in the cloud while your protected health information remains controlled and compliant.
It’s the rare healthcare organization that has the resources to devote solely to security and compliance. But why would they? Most developers and software engineers don’t know compliance, and they don’t want to know. Is this where you want the energy of your organization’s best skill set spent?
By building and deploying safeguards within your infrastructure that meet various regulatory requirements, you can ensure that compliance is not sacrificed on the altar of omission as developers go forth and develop new applications and workloads that have the potential to improve patient outcomes, cure disease and address chronic conditions while better managing costs and competencies. This means developers within healthcare organizations can leverage all the native public cloud tooling at their disposal, while remaining compliant against GDPR, HIPAA, SOC2, GxP, and other regulatory frameworks.
Think of Automated Safeguards as the bumper bowling equivalent of programming and system design. It’s like regular bowling, but the gutters are blocked by rails. From a development perspective, you’re going to get more strikes and fewer gutter balls.
In addition, Automated Safeguards provide two primary type of controls – ones that we put in place to keep something from ever happening and others to alert and remediate if an action occurs that can take you out of compliance. Developers are realizing the liberating powers of innovating in an Automated Safeguard-protected environment. As this usage continues to grow, the requests continue to grow. People are using these tools everywhere they perceive risk. With Automated Safeguards taking on much of the heavy lifting regarding compliance, developers can focus on the healthcare solutions they are trying to bring to market—solutions that are closer to the heart of a healthcare organization’s raison d’être. And even better, with much of the compliance burden lifted, the organization can bring those health-enhancing innovations to market even faster.
It’s a never-ending struggle for healthcare IT organizations to get top talent, so the more they can empower their IT staff to take advantage of the latest and greatest technologies for their core mission, the better. The truth is, healthcare organizations should be able to concentrate on providing the ultimate in products and services for their providers, member, or patients, and offload tangential responsibilities like regulatory interpretations, auditing, and resolution to seasoned specialists.
Request a Demo of ClearDATA Comply
Remove Compliance Consternation and Foster Healthcare Innovation
When you alleviate the fear of compromising sensitive health data and eliminate the burden of managing PHI compliance from on-staff teams, your business is free to pursue new opportunities to advance healthcare and improve patient outcomes. Here are a few examples of some PHI-powered healthcare solutions—that may have not had the chance to see the light of day if scarce resources had to be allocated to compliance expenditures:
- In the underserved behavioral health field, therapeutic virtual reality headsets are being used to track data based on how patients and their bodies react to the visual stimuli within.
- A healthcare IT firm has launched a Google Glass-enabled bedside manner solution that allows a remote scribe to take notes while the doctor gives his or her undivided attention to the patient.
- In an effort to alleviate some of the frustration surrounding the repeated requests of patients to provide personal and health information across different departments and offices, a payer has created a “my data goes where I go” solution.
The High Impact of HITRUST Certification
ClearDATA’s Automated Safeguards for compliance and security are developed within a comprehensive security framework that unifies recognized standards and regulatory requirements from across the entire healthcare industry. Known as the Health Information Trust Alliance (HITRUST), this organization has made it its mission to build information security into the foundation of our industry’s health information systems and exchanges. To validate ClearDATA’s pledge to meet key regulations and protect our clients’ sensitive information, we are HITRUST certified.
To ensure the highest level of safety, the HITRUST certification standards aren’t just woven into the services we offer, but they permeate our administrative practices as well: how employees are on-boarded and off-boarded, how we secure our offices, access privileges and more.
Behind the Curtain: ClearDATA Comply Automated Safeguards in Action
Automated Safeguards can remediate any concerns faster than an application inside an internal IT department. Follow the evaluation/remediation process below and see how we keep healthcare organizations like yours compliant and secure.
See ClearDATA Comply Automated Safeguards in Action
ClearDATA’s Advantage Over the Do-It-Yourself Approach
The time-intensive do-it-yourself method of compliance and security hardly makes sense compared to the capabilities and features of ClearDATA Comply:
- Ongoing interpretations of over 75 state, national and international laws and regulations
- Available for over 70 services across the three major public cloud platforms: AWS, Azure, and GCP
- Over 230 controls automatically in-place across more than forty cloud services
- Each control meets C-Level 1 benchmarks, which averages one hundred applied benchmarks per control
As a customer demand-focused company, ClearDATA is creating more and more Automated Safeguards so developers can innovate safely. In addition, we’ve always been a close collaborator with our major public cloud partners, often brought in well ahead of time, while they’re in the development stage of a certain service. This lets our teams plan accordingly—so once that service launches, the Automated Safeguards tailored to it soon follow.
ClearDATA’s Automated Safeguards for the Big Three Public Cloud Platforms
Amazon. Google. Microsoft. ClearDATA partners with each major cloud player to create Automated Safeguards that allow our customers to use their own tools and processes while still safely deploying sensitive workloads by automating data backup, log backup validation, virus scanning, intrusion protection, and storage volume encryption.


